TODAY, WE’RE PLAYING WITH COOKIES
Cookies are delicious I must admit. Web cookies are delicious I must admit.
We are going to crush it with MD5 and Base64 todaeh
So We’ve given this challenge:
It just said “You don’t have admin access.”
Okay, bye
But no, I’m a female. I’m going to crush dat with girl power
We’re going to search for something with the infamous inspector
F12 if you’re a mozilla firefox slave and we got something quite suspicious from the session section
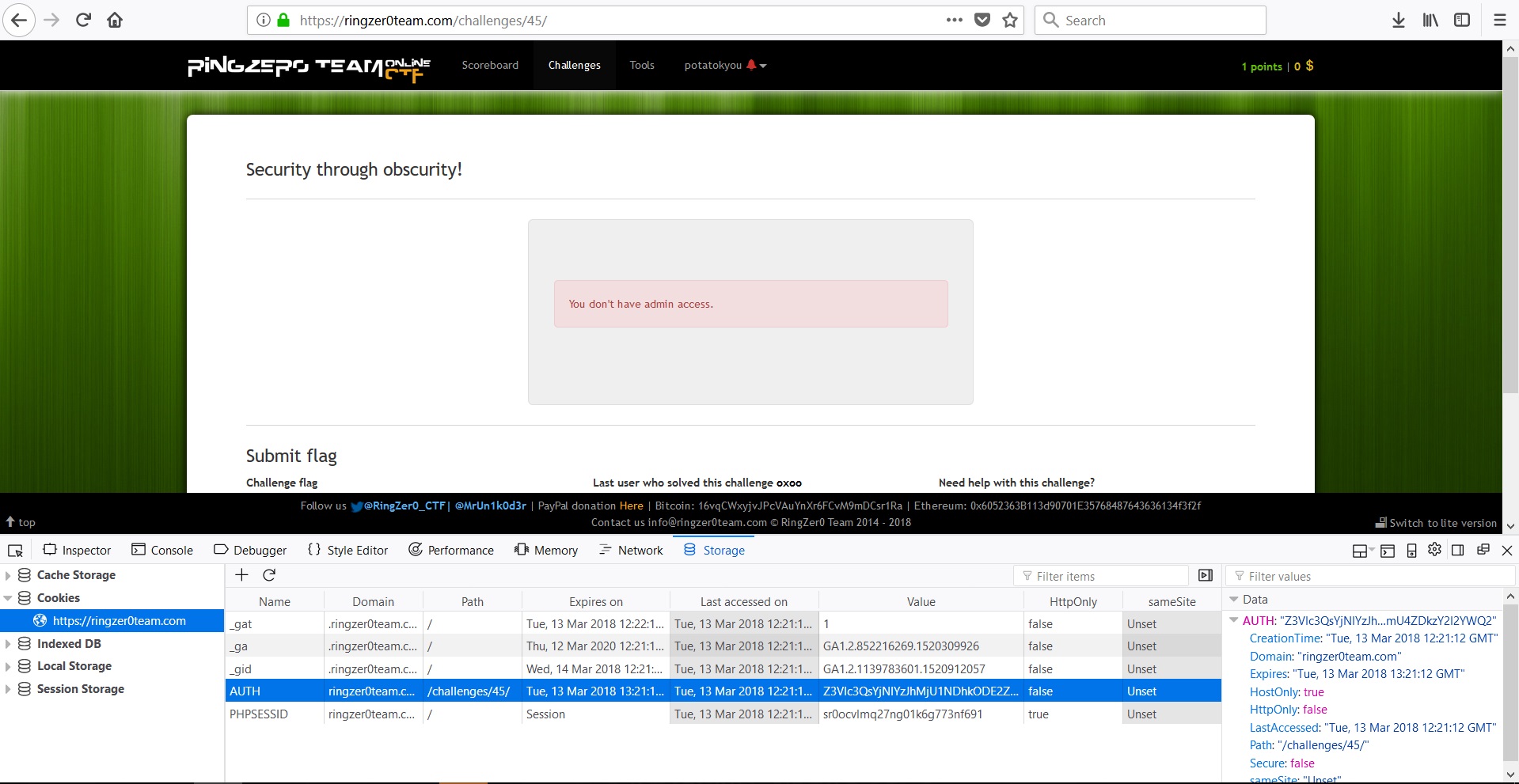 AUTH… hmm… suspicious. It definitely holds authentication informations so let’s copy that value to BASE64 DECODER~ How do I know it was Base64 you ask? welp… I saw the reference…
AUTH… hmm… suspicious. It definitely holds authentication informations so let’s copy that value to BASE64 DECODER~ How do I know it was Base64 you ask? welp… I saw the reference…
REST ASSURED, we got this thingy from that Base64 decoder:
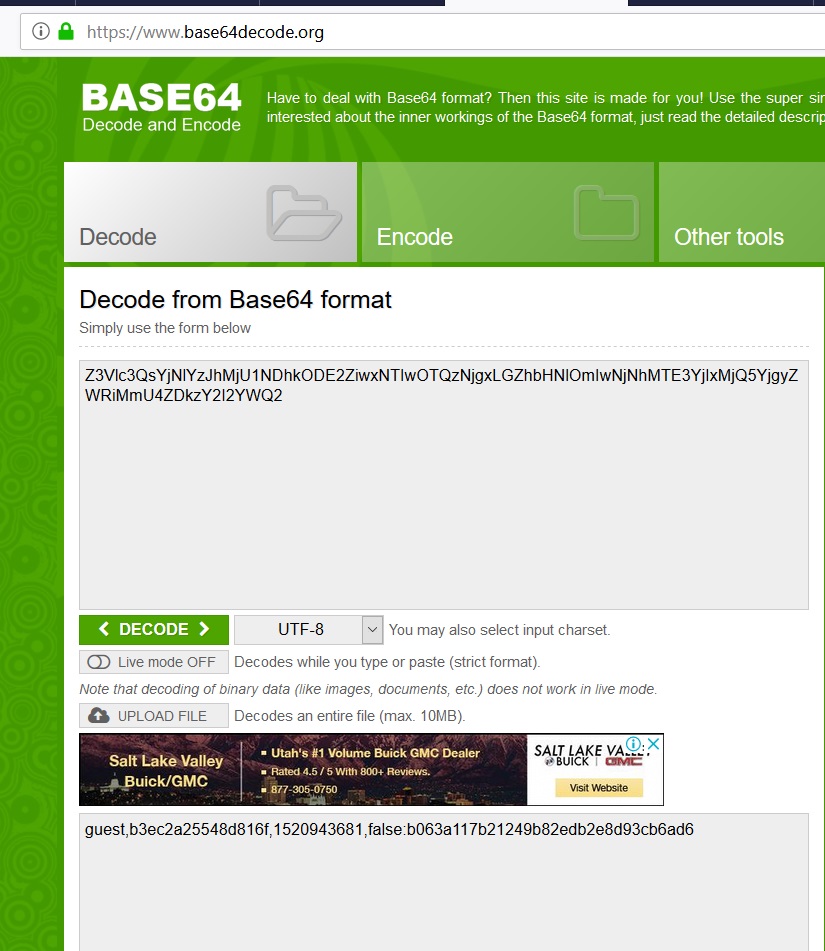
guest,b3ec2a25548d816f,1520943681,false:b063a117b21249b82edb2e8d93cb6ad6
WHAT ARE THOOSEE?~
Apparently
guest is our status right now,
b3ec2a25548d816f seems like it’s randomly generated,
1520943681 is a UNIX time,
false is what we need to change into true, and
apparently b063a117b21249b82edb2e8d93cb6ad6 is the md5 of everything starting from guest to false
Okay let’s get working
change guest into admin
don’t change b3ec2a25548d816f
if you work slowly, change the UNIX time to any time faaaar away from now
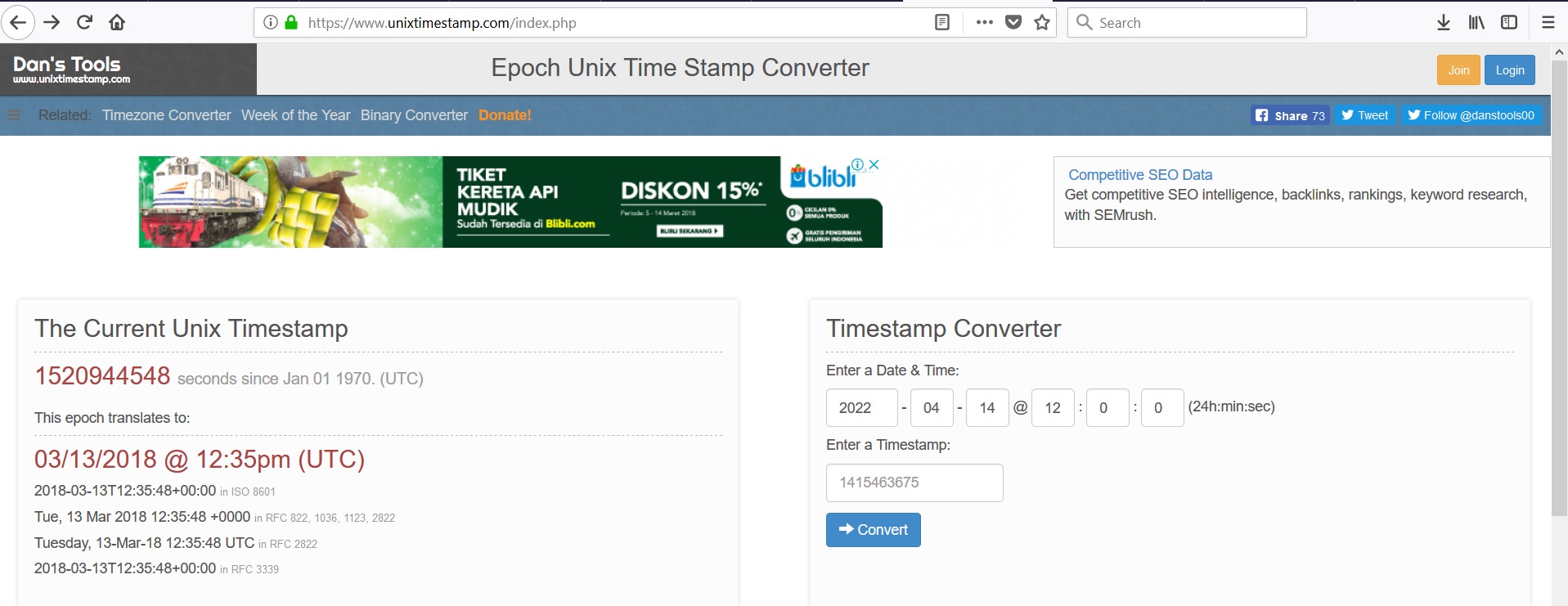
I like it too far to 2022 bcoz I’m such a drama queen. Convert that and we got this
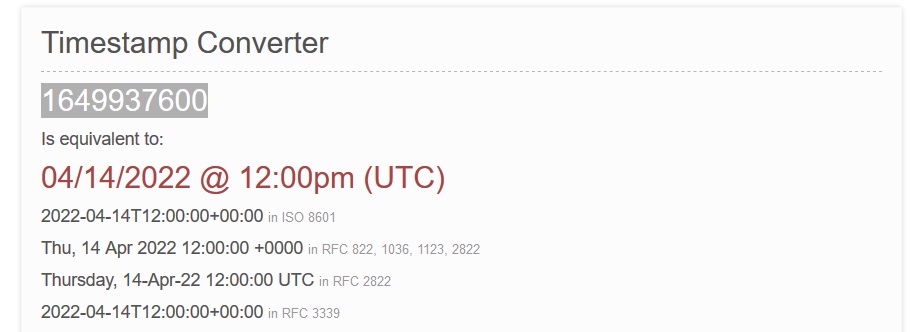
Okay, change the UNIX time with that.
change false to true
and lastly, MD5 everything from guest to false including the comas.
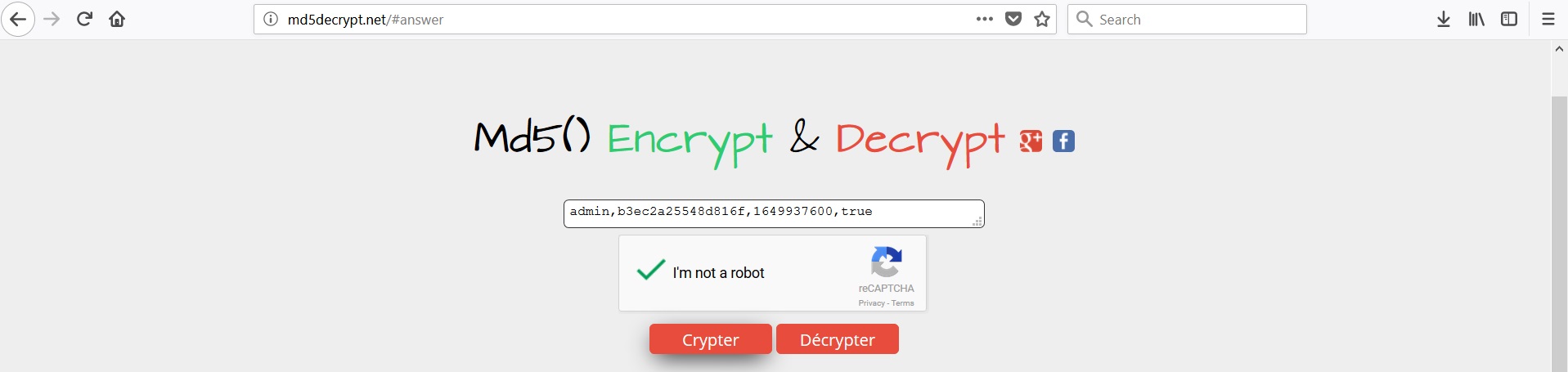 Crypter~
Crypter~
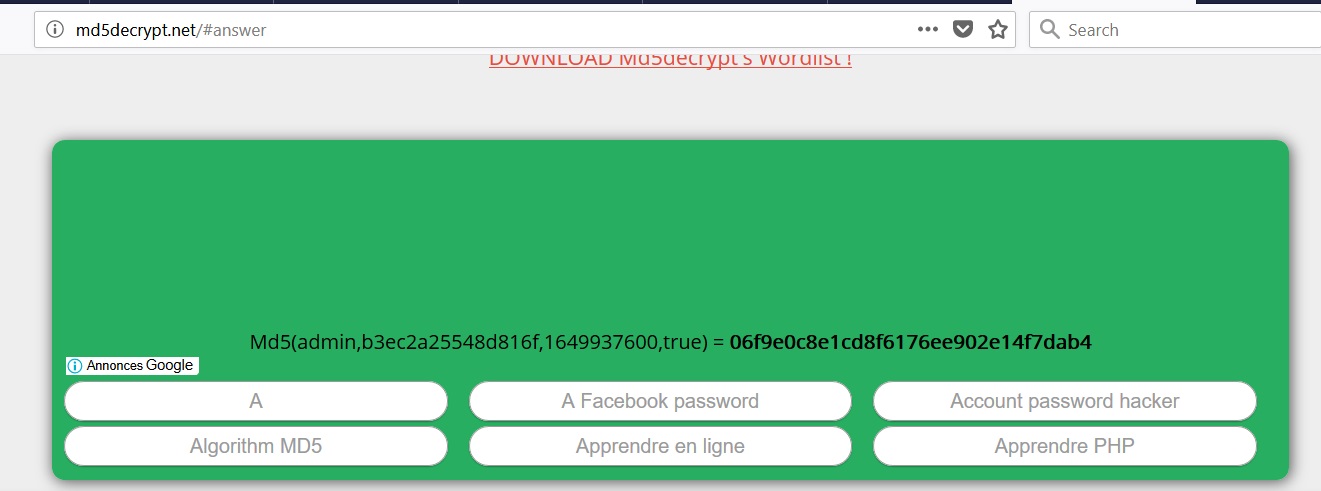 Okay, copy that all and integrate it with what we got earlier.
Okay, copy that all and integrate it with what we got earlier.
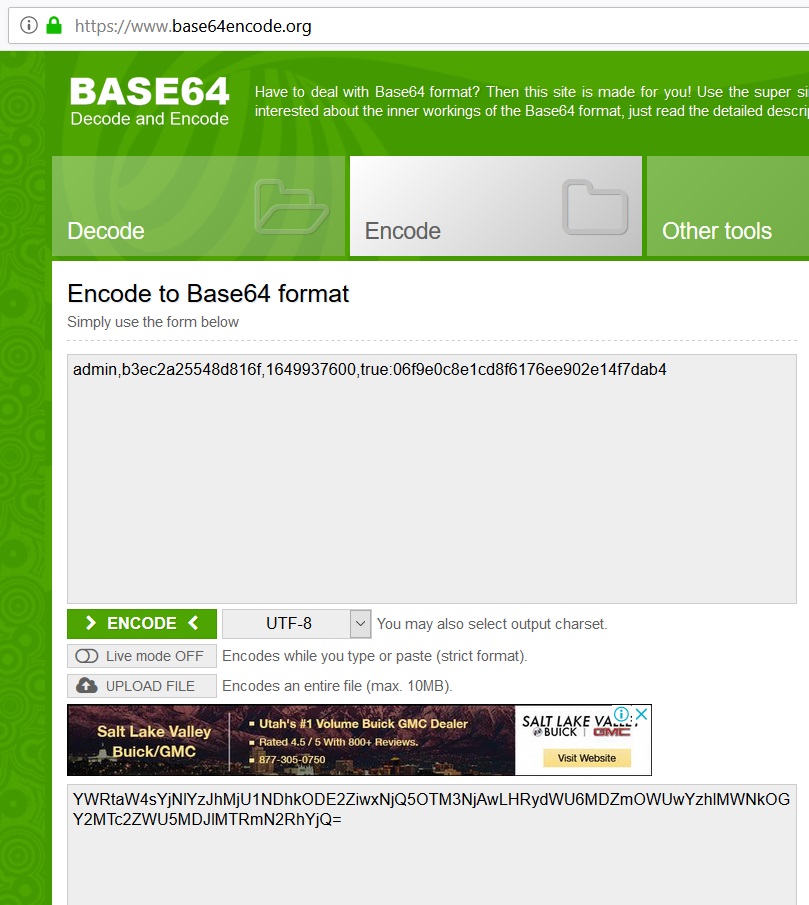
Okay, that Base64 is fixed.
Copy them all and paste it where it belonged and refresh the page and you’ll get this:
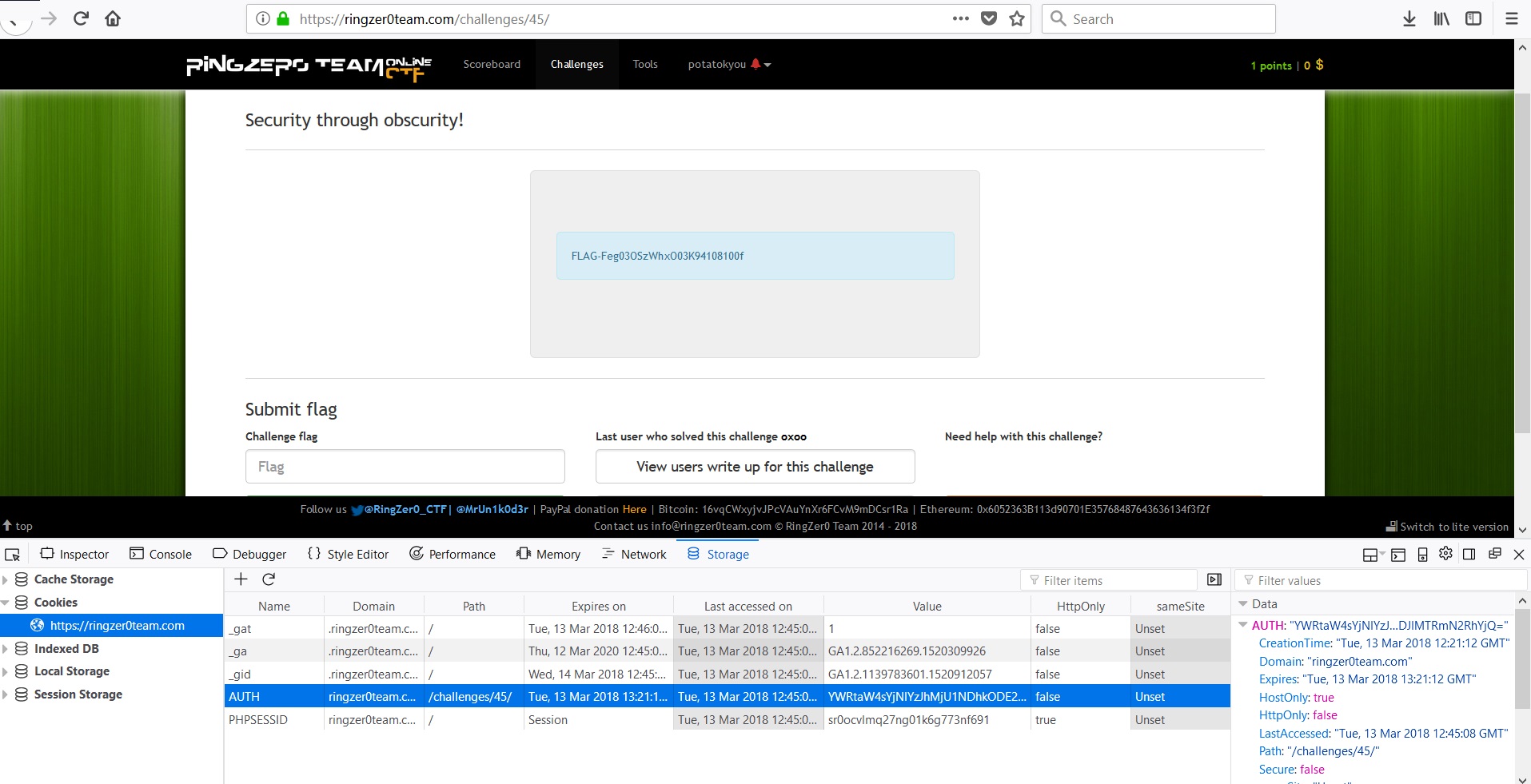 Woohoo~ That’s the flag~
Woohoo~ That’s the flag~
Enough talking, goodbye!
Reference: https://github.com/professormahi/CTF/blob/master/ringzer0team/Web/Security%20through%20obscurity/Area51.markdown Challenge: https://ringzer0team.com/challenges/45/ Tools used: https://www.base64encode.org/ https://www.base64decode.org/ http://md5decrypt.net/ https://www.unixtimestamp.com/
